Using Password4j And The BCrypt, SCrypt, And Argon2 Password Hashing Algorithms In Lucee CFML 5.3.7.47
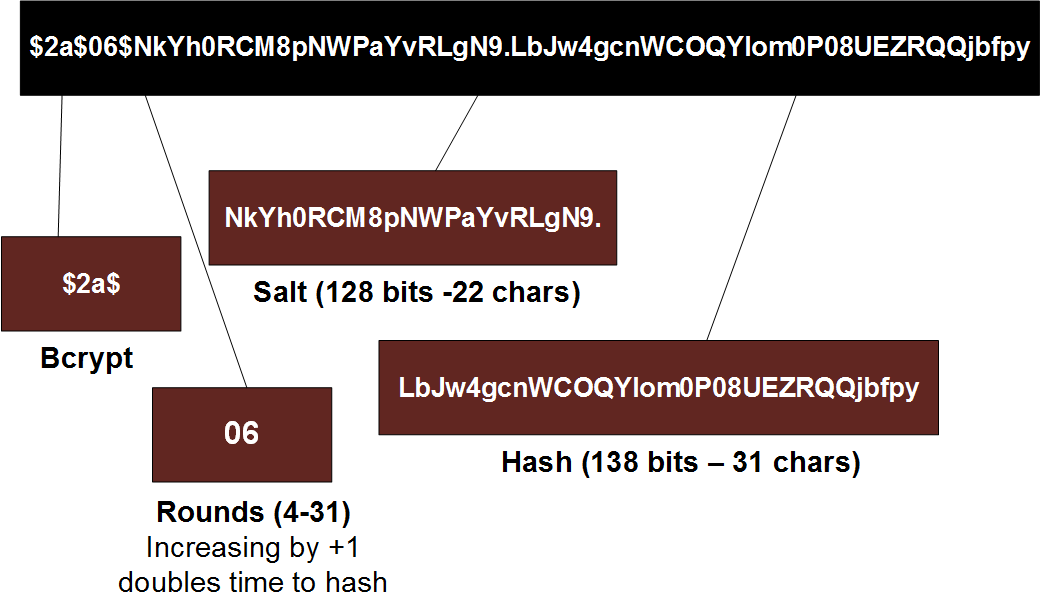
![PDF] High-speed implementation of bcrypt password search using special-purpose hardware | Semantic Scholar PDF] High-speed implementation of bcrypt password search using special-purpose hardware | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/b786995e010571b1c86405f816af227fd83ad44f/3-Figure1-1.png)
PDF] High-speed implementation of bcrypt password search using special-purpose hardware | Semantic Scholar
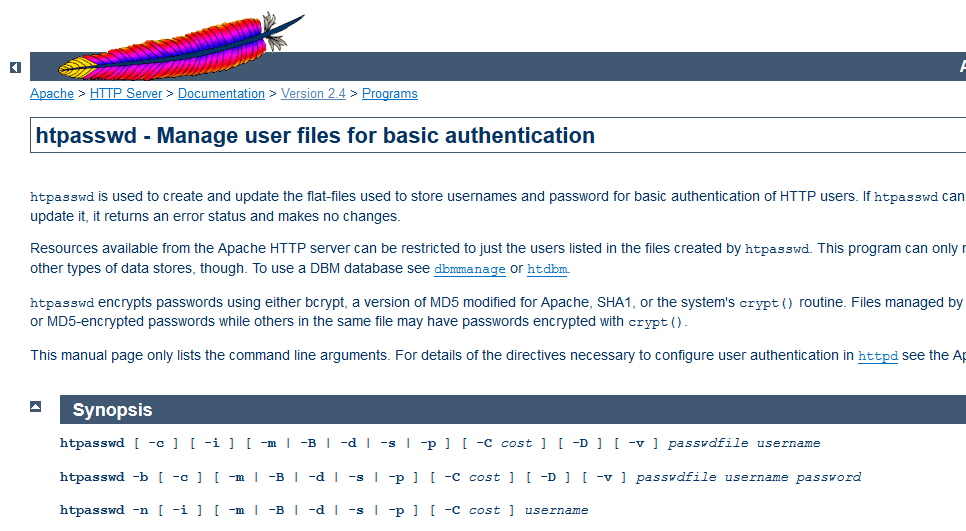
Create password credentials for htaccess and htpasswd files - HTPasswd Generator | Web 2.0 Generators
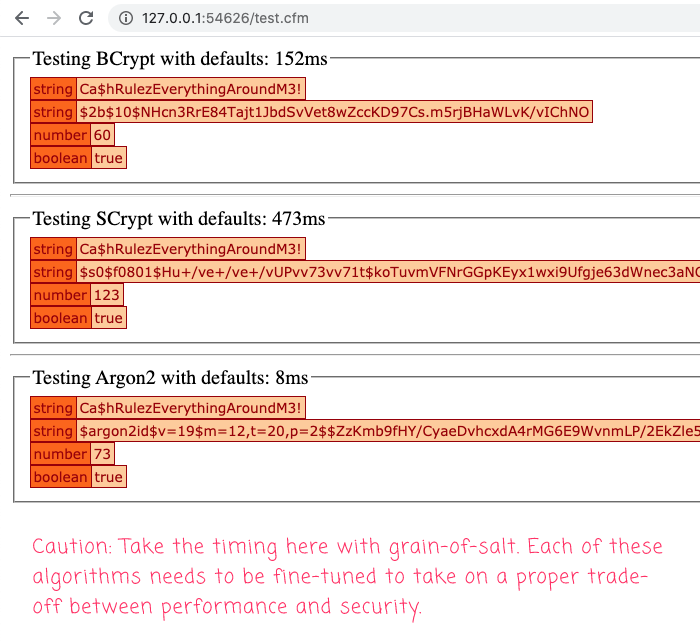
How to interpret the scrypt vs bcrypt vs pbkdf2 comparison table? - Information Security Stack Exchange

Passwords and hacking: the jargon of hashing, salting and SHA-2 explained | Data and computer security | The Guardian