Virus Bulletin on Twitter: "Check Point draws attention to a new Android trojan named “FakeCalls”, a voice phishing (vishing) malware that is able to masquerade as more than 20 financial applications and

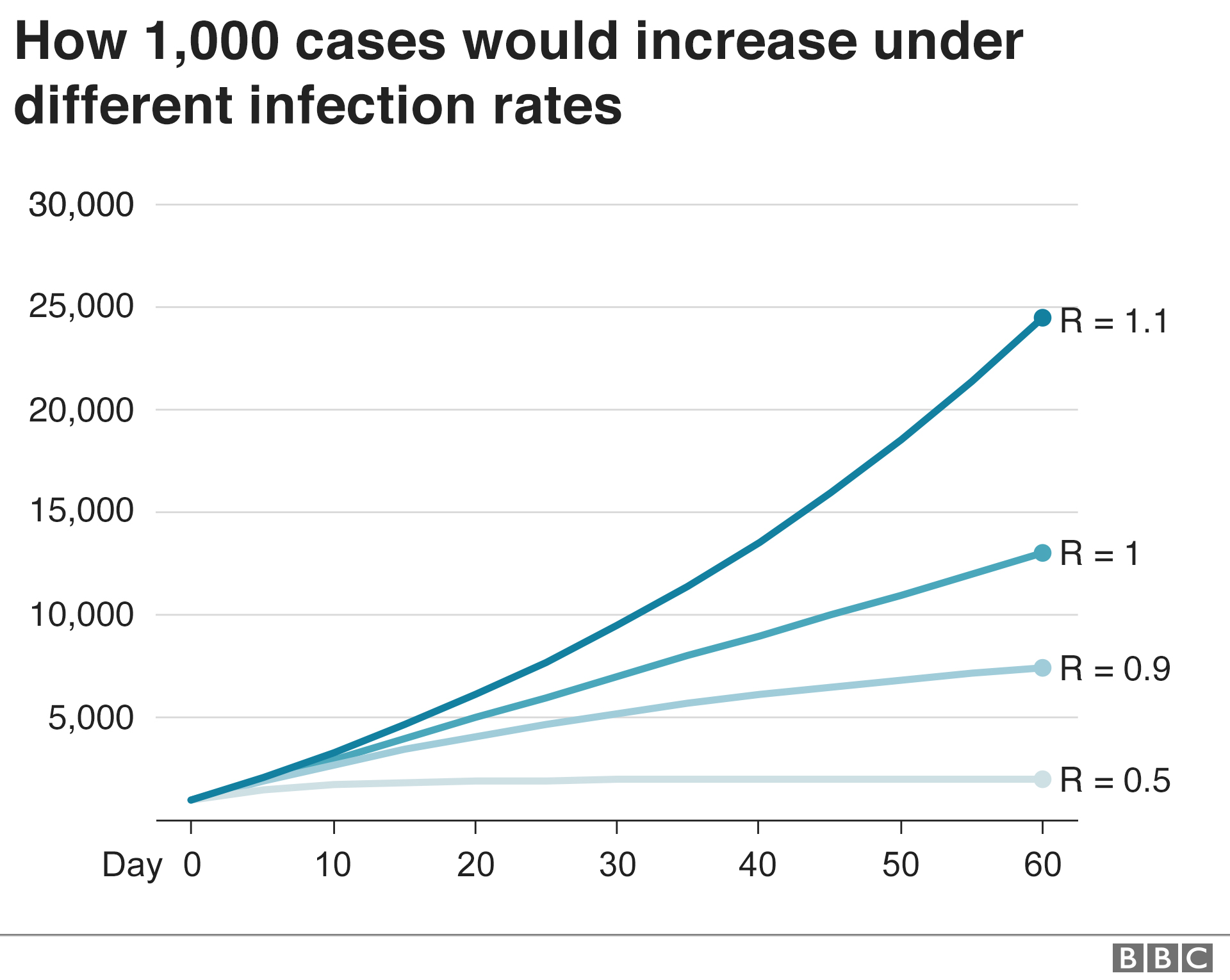
Virus particle propagation and infectivity along the respiratory tract and a case study for SARS-CoV-2 | Scientific Reports
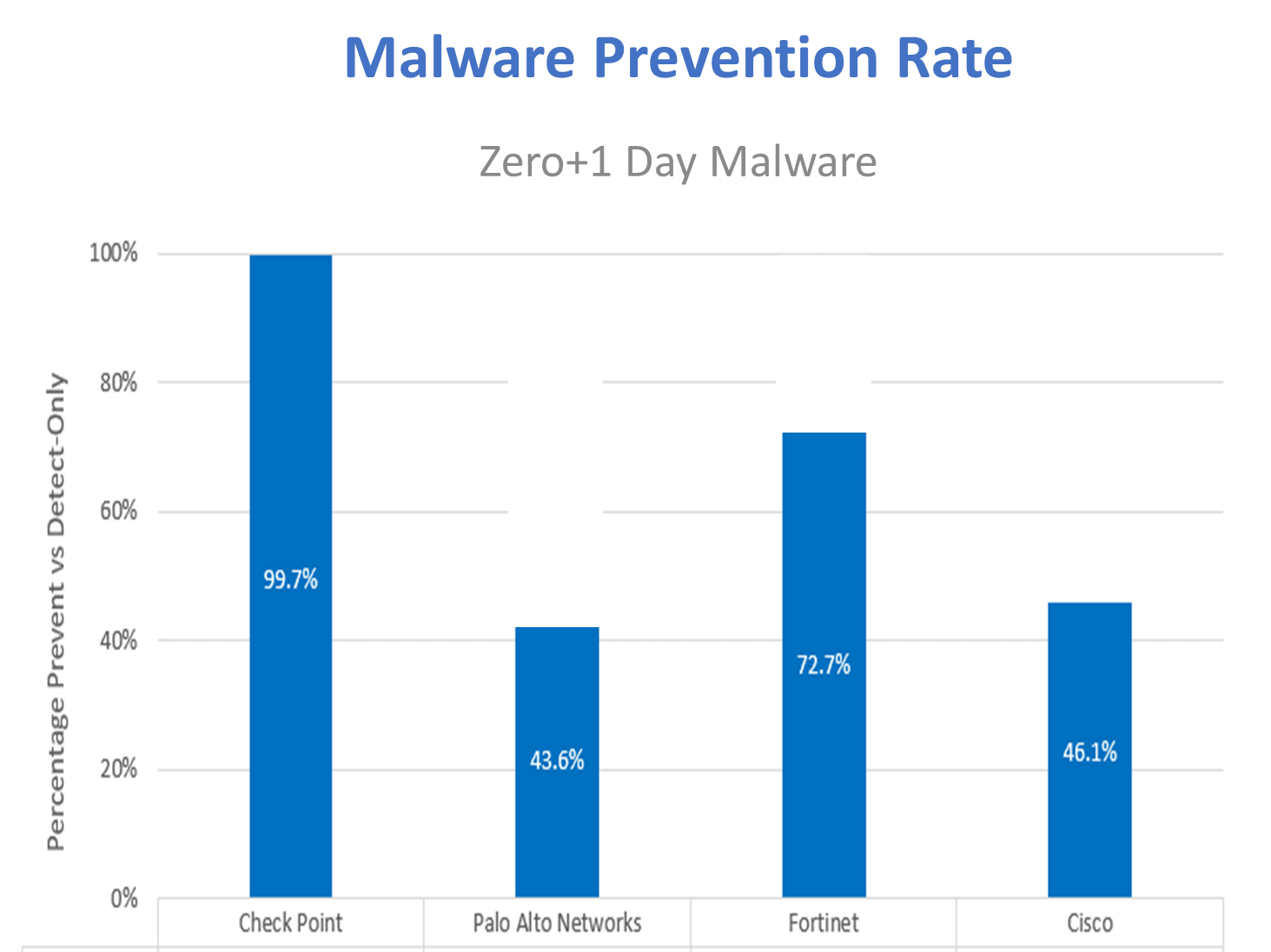
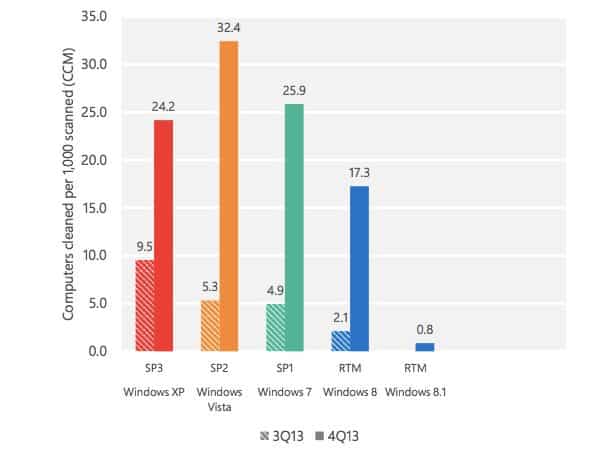
Check Point Software takes 1st Place in Independent Test of Top Network Firewalls - Check Point Software
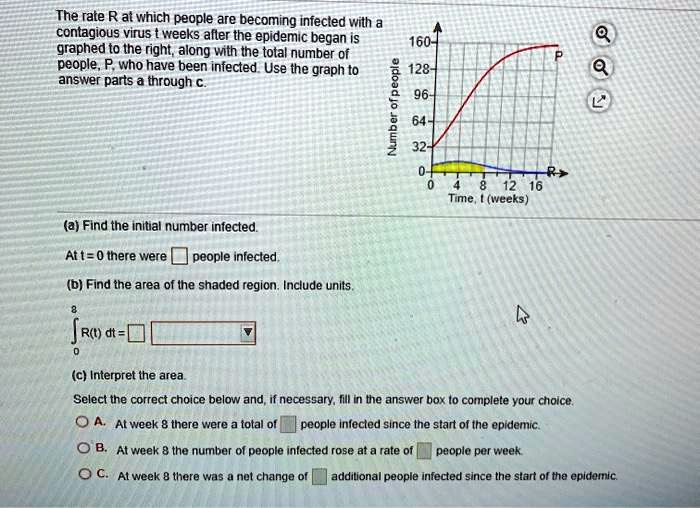
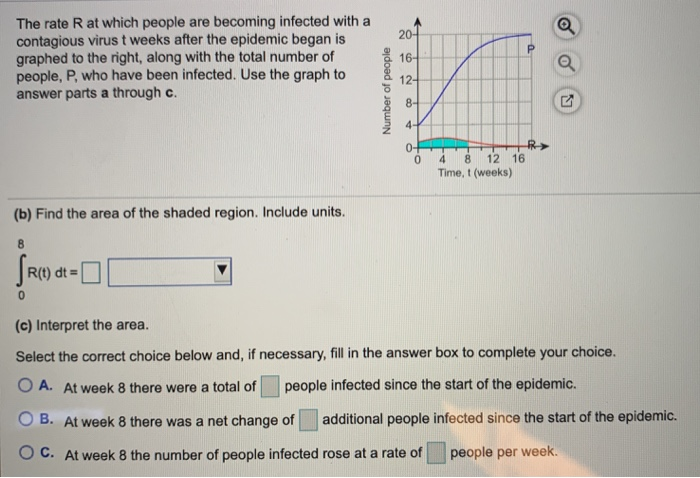
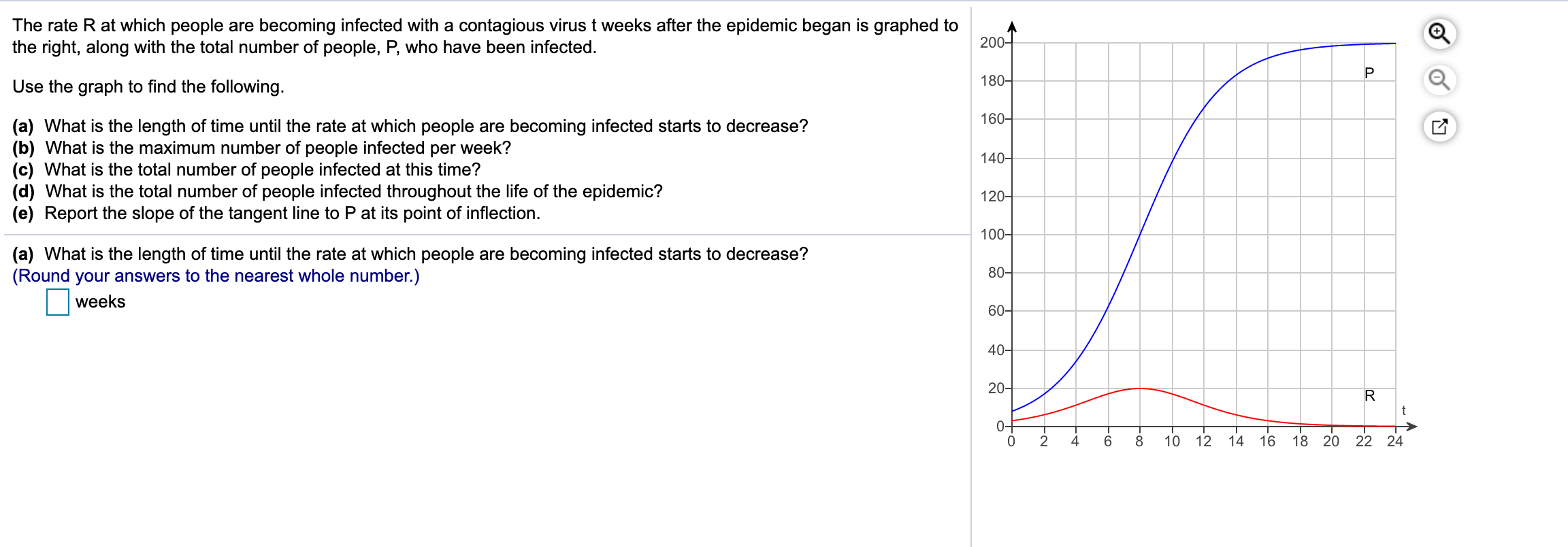
SOLVED: The rate R at which people are becoming infected With a contagious virus t weeks after the epidemic began is graphed to the right; along with the total number 0f 160
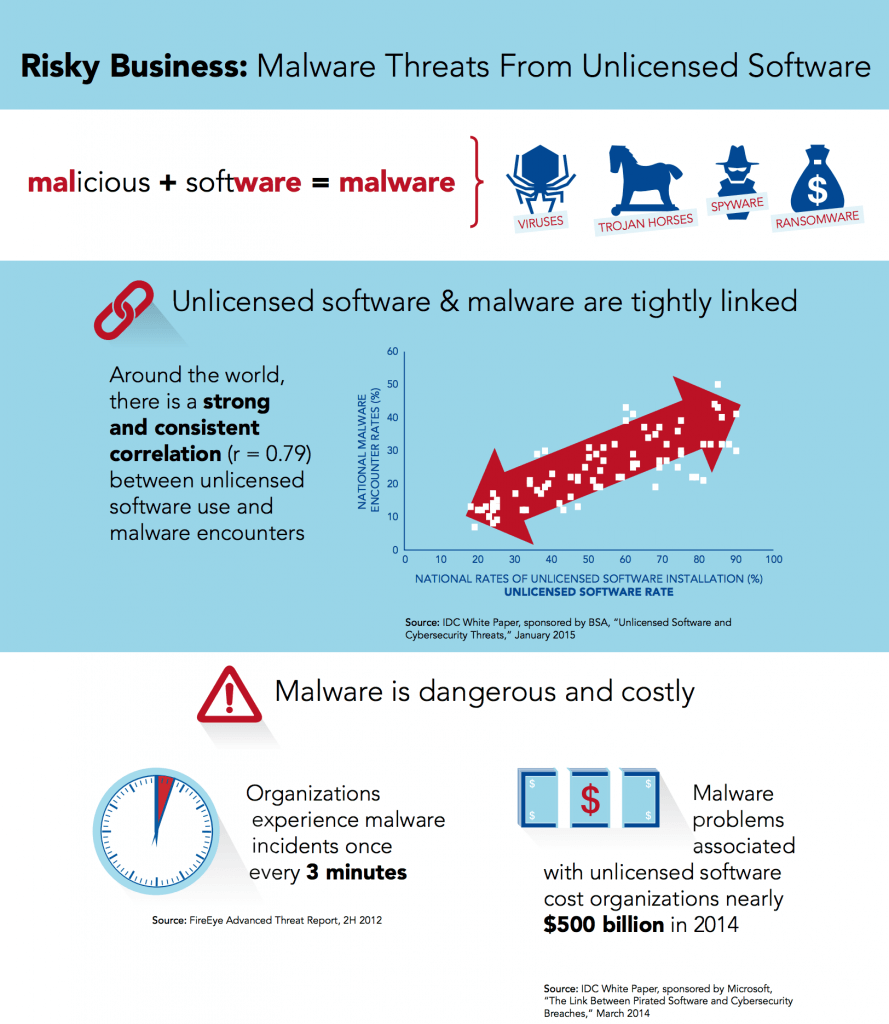
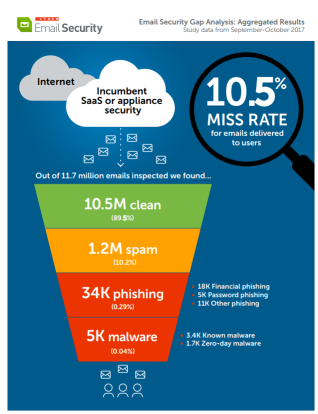
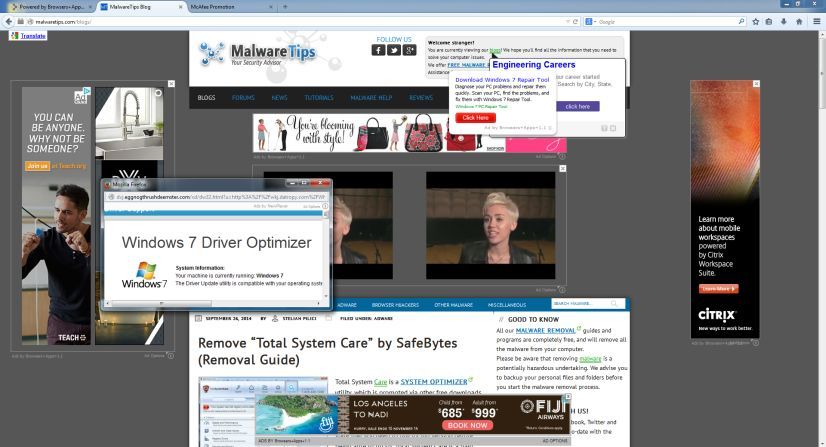
Malware Threats from Unlicensed Software: The Critical First Step for Cyberrisk Management | BSA TechPost
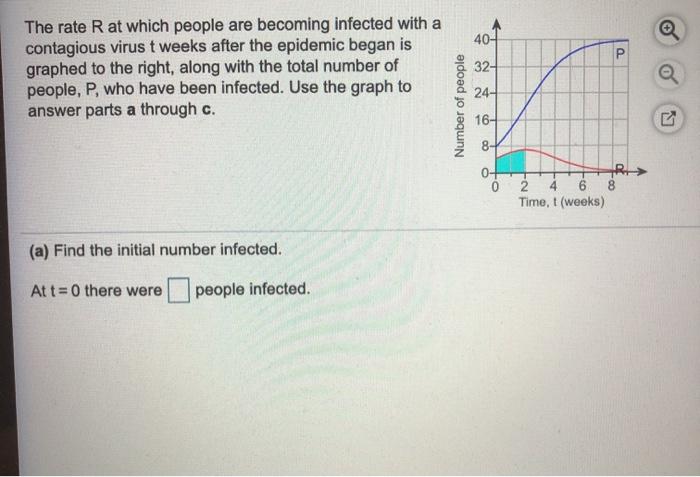
SOLVED: The rate R at which people are becoming infected with a contagious virus weeks after the epidemic began is graphed to the right; along with the total number of 1 people;

Vaccine news stories hosting malware disseminated across Spanish-language Twitter – Federation Of American Scientists
Temperature modulates dengue virus epidemic growth rates through its effects on reproduction numbers and generation intervals | PLOS Neglected Tropical Diseases
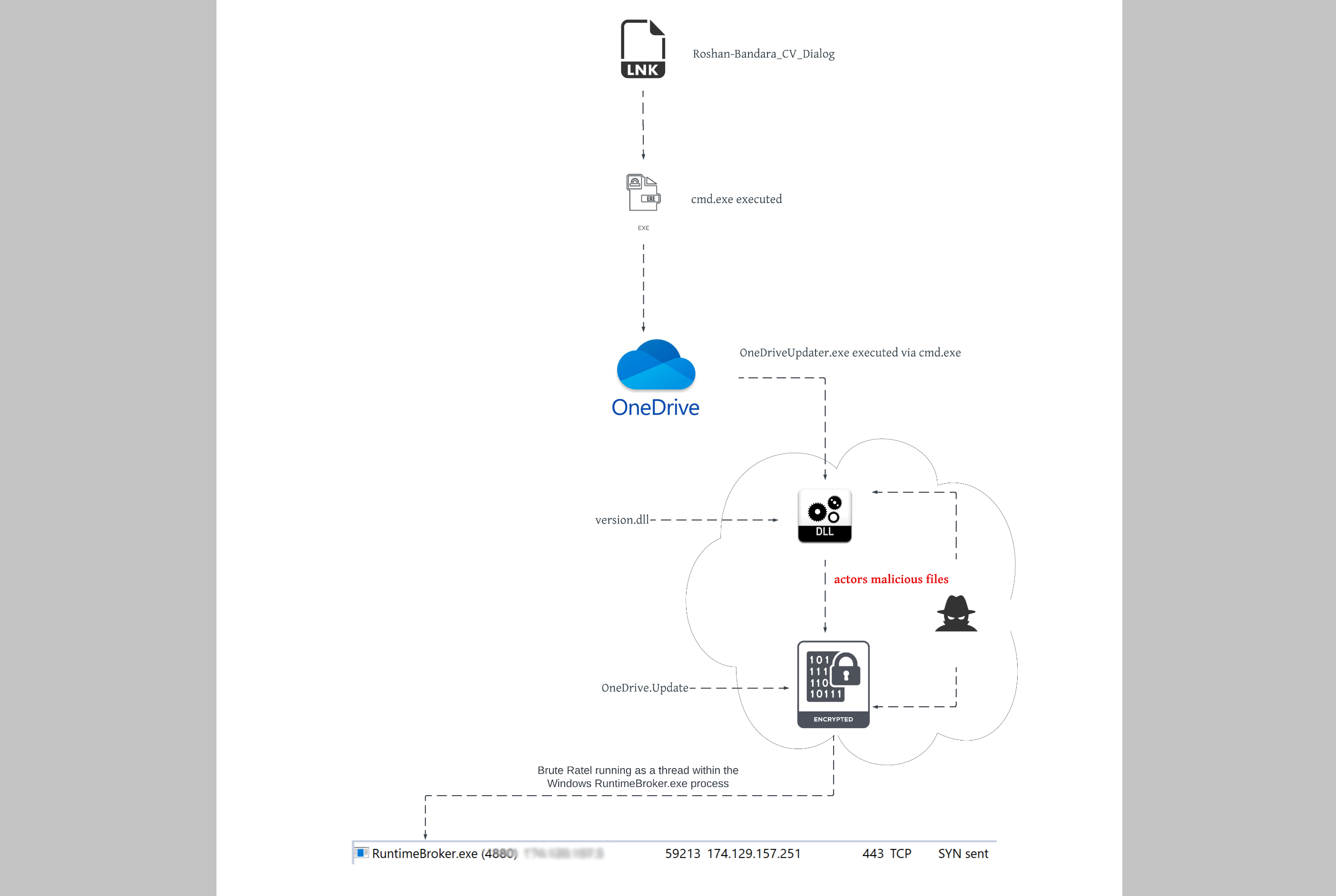
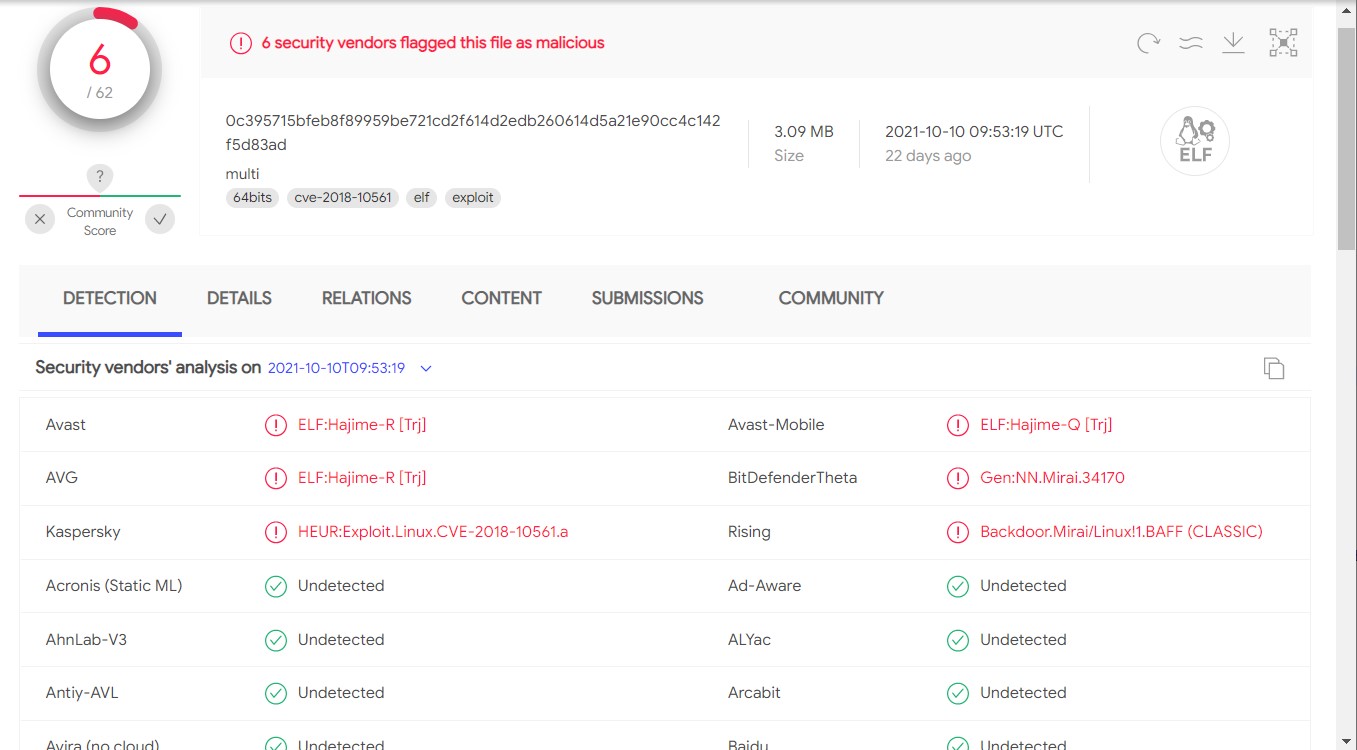
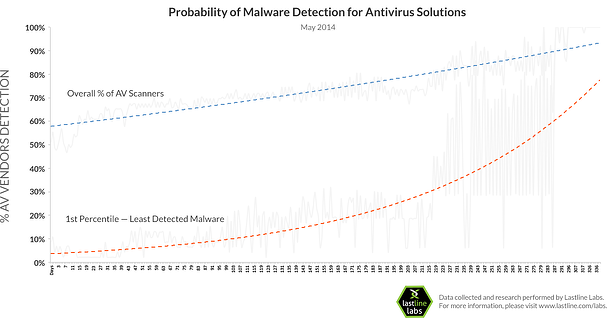
Researchers Discover Dangerous Malware That Can't Be Detected By 50+ Antivirus Products / Digital Information World